We are one of the few Security companies that decided to support ECC SSL Certificates with stronger security and 2x times higher performance.
ECC vs RSA
ECDSA, Being a very efficient algorithm allows much smaller key sizes with stronger encryption. For example, a 160 bit ECC key is comparable with an RSA 1024 bit.
The table below illustrates how efficient is the ECDSA algorithm:
| Symmetric Key length | RSA Key length | ECC Key length |
|---|---|---|
| 80 bit | 1024 bit | 160 bit |
| 112 bit | 2048 bit | 224 bit |
| 128 bit | 3072 bit | 256 bit |
| 192 bit | 7680 bit | 384 bit |
As ECC is a relatively new approach in cryptography, and it is not supported by older programs and operating systems. ECC SSL Certificates are not supported by Internet Explorer 7 in Windows XP. However, it should not be a issue, as windows xp users that are using Internet Explorer version 7 or lower is a limited number of users.
The following table illustrates the main differences between RSA and ECC:
| RSA | ECC |
|---|---|
| RSA is the first practical public-key cryptosystem and it's widely use | ECC is the most powerful algorithm with the best performance |
| 2048bit is the recommended key size for RSA | prime256v1 is the recommended prime for ECC |
| RSA cryptosystem is supported by most operating systems and programs | It uses much smaller and faster keys than RSA cryptosystem |
| RSA is slower and requires more processing power | ECC is not supported by Internet Explorer 7 in Windows XP |
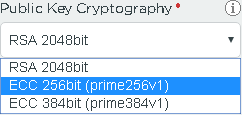
How to order ECC Certificates?
Any Comodo SSL certificate has ECC support. Symantec Secure Site Pro EV also supports ECC. To use a ECSA encrypted key instead of an RSA key, select the ECC algorithm during CSR generation.